Notícias
UniSat inscription indexing challenges and lightweight wallet discovery for collectors
Verify Access control must include multi-factor authentication and strict device attestation for any system that interacts with signing devices. If a custodian issues off-chain claims backed by on-chain reserve entries, settlement requires reconciliation between the custodian and the shielded ledger state. State channels and payment channels are useful for repeated bilateral or hub-mediated transfers. Crosschain […]
Leia maisHow NEAR Protocol (NEAR) explorer telemetry can aid BTSE compliance and analytics
Verify Integration should not introduce confusing UX that could lead to user errors or support overhead. When interacting from an exchange interface, double check that the exchange supports the specific token standard and chain version used by the staking contract. Contracts should specify indemnities for losses arising from custodian negligence, thresholds for acceptable downtime, and […]
Leia maisRegulatory compliance checklist for ERC-20 token issuers operating across multiple jurisdictions
Verify In the end, bridging brings valuable interoperability, but it imposes quantifiable privacy costs that must be weighed against the utility of cross‑chain access. During fast moves this can be exploited by arbitrage bots and flash loans to extract value or to create artificial scarcity. Scarcity matters, but scarcity is framed by protocol rules and […]
Leia maisHow Jaxx Liberty wallet integrations influence Total Value Locked across chains
Verify Always test the process with a small amount first, keep software and node endpoints updated, and consult Guarda’s official help resources and the specific blockchain’s documentation for any chain-specific parameters, gas settings, and best practices before committing large balances to staking. Tokenized access can gate premium content. Content-addressed storage and cryptographic hashes remain foundational. […]
Leia maisSecuX hardware integration with Zap protocols for streamlined cold staking operations
Verify Comparing market cap to protocol engagement measures such as daily active wallets, time-weighted user retention, and in-game transaction volume reveals whether headline valuation corresponds to real utility or speculative froth. When you build a multisig wallet, add each cosigner as a separate device. The device should operate in an air-gapped mode and accept transaction […]
Leia maisEvaluating Prokey and Optimum Hardware Wallet Compatibility Risks
Verify Independent privacy and security reviews will catch subtle leaks and improve trust. For collectible items, bonding curve pools help stabilize pricing and discovery. Token discovery methods must adapt to new chain designs, privacy techniques, and attacker tactics. Cross-chain tactics can augment returns. If BitFlyer were to custody wrapped TRC-20 LTC or underlying Litecoin reserves, […]
Leia maisUsing Portal liquidity rails to optimize Frax Swap routing and slippage control
Verify At the same time, liquidity depth still depends on where market makers choose to place capital. Apply least privilege to agent processes. Each shard processes transactions in parallel. Parallelism in block verification and compact block propagation improve sync latency for nodes that still validate blocks, but they increase CPU and memory demands during initial […]
Leia maisExamining Flare (FLR) burning mechanism impacts while using O3 Wallet for custody
Verify These runtimes let apps maintain mutable state while anchoring authoritative events permanently. For institutional and high-net-worth clients, cold storage remains the backbone of custody: multisignature vaults, hardware security modules, and geographically distributed key shares reduce single points of failure. Failure to do so risks customer confusion and increased support burdens, especially around lost-key scenarios […]
Leia maisOptimizing borrowing strategies across Joule and Kinza Finance liquidity pools
Verify Many protocols mint tokens that track staked ether or other assets and let users move or trade these tokens freely. When an error occurs in production, prioritize a safe halt and reconciliation. Regular reconciliation of exchange deposits and withdrawals reduces uncertainty and improves the signal-to-noise ratio for meaningful alerts. Keep alerts for sequencer announcements […]
Leia maisHow Layer 3 startups attract venture capital when listing through CEX.IO gateways
Verify VCs want clear scenarios for secondary markets, buyback programs, or token‑for‑equity swaps. Operational practices reduce many risks. To mitigate risks, teams should run independent watchers. Automated watchers that verify L2 state roots against canonical L1 checkpoints and that alert multisig signers when anomalies appear are critical components. For memecoins this means additional monitoring of […]
Leia maisInterpreting Orca Total Value Locked Fluctuations And Their Signal For Liquidity Health
Verify Users do not receive CDIC‑style deposit insurance on crypto. Use the S1 for all signing steps. These steps reduce common operational risks but do not eliminate all smart‑contract and human threats, so maintain vigilance and follow official Electroneum and MEW security guidance. Seek compliance guidance when operating on regulated venues and maintain transparent reporting […]
Leia maisAssessing OKX Web3 Wallet Support for ERC-404 Token Standards and UX Impacts
Verify The ecosystem will keep evolving as both attack techniques and prover technologies improve. Early participants get larger rewards. Rewards denominated in native or governance tokens complicate accounting. Predictable gas accounting and composability at the Layer 1 level also make it feasible to implement complex on-chain credit middleware—credit scoring oracles, modular risk adapters and composable […]
Leia maisAnalyzing ViperSwap Pool Composition and Impermanent Loss Scenarios for LPs
Verify Practices that matter include cryptographic signing of firmware images, secure boot chains anchored in immutable hardware, reproducible builds that let third parties verify binary provenance, and clear, documented procedures for over-the-air updates and emergency rollback. Transactions on Stacks are public by design. System designers can adopt several pragmatic mitigations. Practical mitigations include conservative LTV […]
Leia maisEvolving mining economics and hashrate distribution in decentralized networks today
Verify Operational tradeoffs include bridge trust assumptions, latency from challenge periods, and complexity of dispute resolution. When interacting with rollup ecosystems, prefer bridges that are trust-minimized and audited, but recognize that many implementations remain custodial in practice. In practice, the most robust expectation is conditional rules and hybrid mechanisms. Incentive mechanisms and slashing policies encourage […]
Leia maisPractical steps Pionex can take to reduce AML false positives and friction
Verify Users who prioritize convenience and fiat rails may prefer custodial exchange accounts. It favors discoverability and quick wins. Digital twins of networks enable scenario planning without risking mainnet health. A healthier metric acknowledges that not all tokens are equally available to be bought or sold without moving the price. Smart contract based schedules are […]
Leia maisEvaluating Mux Protocol use cases in DePIN deployments for real-world connectivity
Verify The combination of tailored curation, thoughtful sale mechanics, enforced vesting, and ongoing incentives helps align incentives across founders, investors, and community members. For certain quantitative strategies, AI can materially improve signal-to-noise ratios and enhance portfolio diversification. Diversification across multiple signal providers and LSD issuers mitigates single-point dependence. Dependence on a single DA provider increases […]
Leia maisAssessing RabbitX orderbook integration with MEXC for Web3-native liquidity routing
Verify When you need to authorize a transaction, use MyEtherWallet to prepare the transaction and then sign it with a connected hardware device. Какой смысл «SC» выбрать? Avoid obscure or abandoned apps. Fitness apps can accept GMT as payment for subscriptions or partner services, and third-party platforms can reward activity with GMT-backed incentives. It can […]
Leia maisTestnet Deployment Lessons From Decredition When Implementing ZK-Proofs
Verify MEV and front-running add practical risk to liquidation engines. Compare minted events with totalSupply. When auditors open a Web3 blockchain explorer to inspect STORJ storage token activity they typically begin at the token contract page, where the token tracker aggregates on-chain facts such as the verified source code, the contract address, the token symbol […]
Leia maisDesigning sustainable rewards for Proof-of-Stake staking pools under variable inflation
Verify Keep those runbooks accessible to the on-call team and test them in drills. Economic disincentives are layered too. Tooling vendors will need to invest in abstraction layers and clear migration paths to maintain trust. More trust-minimized patterns seek to rely on light clients or on-chain verification of proofs produced by source chains, but such […]
Leia maisSandbox Tokenomics After Halving And Implications For Liquid Staking Markets
Verify Increased on-chain activity related to reallocation and cross-pool arbitrage has also contributed to transient congestion and failed transactions during volatile windows. This reduces single-point deanonymization. Any integration effort must consider how each design choice changes the attack surface for deanonymization and must prioritize designs that keep custody operations opaque to analytics while remaining usable […]
Leia maisDesigning tokenomics for low-liquidity projects to avoid hyperinflationary collapse risks
Verify These include stronger wallet management with a greater share of assets placed in cold storage, more rigorous withdrawal controls, mandatory KYC and AML screening, and multilayer authentication options for users. For Solana swaps, leverage Jupiter’s quote and route APIs to construct transactions server-side or client-side before asking a wallet to sign. Off-chain signals like […]
Leia maisConfiguring Xverse wallet for secure multi-chain interactions and permissioned decentralized apps
Verify These dynamics concentrate initial token ownership in entities able to pay for priority or to collude with miners, which undermines the egalitarian narratives of many launches. For forks, start from the exact snapshot rules and inspect whether replayed balances were subsequently claimed, burned, or migrated; unclaimed forked tokens are often illiquid and should be […]
Leia maisHow NULS wallet performance interacts with CoinDCX throughput bottlenecks
Verify Station should set clear fee rules and transparent reporting for depositors. Treat each contract as a public interface. Standard interfaces for compliance attestations help interoperability. Interoperability and user experience must be validated. When a Flow contract emits an event, the relayer verifies the event and then submits a corresponding transaction to Besu, or vice […]
Leia maisHow Blur (BLUR) marketplace mechanics create new metaverse trading patterns
Verify Address clustering and entity labeling reduce false positives by identifying known exchanges, bridges, and large custodial wallets. By treating yield farming as a complex, dynamically correlated portfolio problem, practitioners can pursue superior long-term outcomes while reducing the probability of catastrophic losses. Use stop-losses that take into account real liquidity bands rather than fixed percentages, […]
Leia maisOptimizing developer workflows using Frame wallet integrations for local smart contract testing
Verify An exploit or malicious upgrade in a seemingly peripheral protocol can propagate into the entire strategy stack. For example, options, leveraged pools, or lending markets that use HMX as collateral require reliable price discovery and execution depth that thin markets cannot provide. RPC providers under load return inconsistent receipts. Standardised receipts and settlement proofs […]
Leia maisTangem Web Integration Challenges for Hardware Wallets and Web dApp Compatibility
Verify Some exchanges choose to delist tokens in certain jurisdictions rather than maintain segregated operational controls, while others build complex localized compliance stacks to retain global coverage. In your desktop wallet select send, paste the copied Bithumb deposit address, and enter a small test amount that is above the exchange’s minimum deposit but small enough […]
Leia maisOn-chain analysis of BTC tokenomics and Bitcoin Core fee market dynamics
Verify The Cardano ledger model is unique. When NFTs follow common standards, it becomes easier to build automated market makers, index pools, and fractional vaults. Using Unchained Vaults to optimize yield across multiple chains brings real benefits and real hazards. Chain-specific hazards such as deep reorganizations, censorship, or validator collusion on either Harmony or the […]
Leia maisHow Sender Labs venture capital participation accelerates cross-chain tooling adoption and growth
Verify Continuous monitoring of holder concentration, fee regimes, and relayer economics helps make timely adjustments. When liquidity is ample, incremental burns can proceed; when depth falls below predefined thresholds, the mechanism pauses or shifts toward accumulating reserves rather than immediate destruction. Retiring keys must follow verifiable destruction procedures. Weak operational procedures, inadequate separation of duties, […]
Leia maisDesigning Play-to-Earn token sinks and anti-inflation mechanics for sustainable economies
Verify False positives can block legitimate customers and false negatives can miss laundering. If price feeds are compromised, automatic burns can be triggered incorrectly. Block explorers are convenient aggregators but can misrepresent state when indexers lag, when multiple token contracts with similar symbols exist, or when metadata and token decimals are cached incorrectly. Snapshot and […]
Leia maisOptimizing Kukai wallet workflows for user-friendly Tezos token management
Verify Back up your seed phrase on a physical medium and store that backup in a secure, offline place. When a user receives tips, subscriptions or creator tokens denominated in an algorithmic stablecoin, they avoid the cognitive overhead of chasing volatile token prices while still benefiting from onchain composability. However, richer composability also increases systemic […]
Leia maisBest practices for running yield farming strategies from a Lisk desktop environment securely
Verify Gas abstraction and payment options for relayers can lower the operational overhead of microtransactions that devices might require, and templates for common DePIN operations reduce cognitive load for new staff. In short, hardware-backed key management with Tangem-style devices offers strong cryptographic guarantees and practical integration for institutions. Institutions, index providers and regulators must adapt […]
Leia maisIntegrating Verge-QT wallet support with optimistic rollups to improve lending UX
Verify In Android, side loaded apps can request broad permissions. VCs look for realistic monetization paths. All signing paths must be auditable and produce non-repudiable logs. Audit logs and external attestations support post-rotation verification. When contributor teams or community members propose changes to the codebase they often target privacy features such as transaction obfuscation, address […]
Leia maisSonne Finance interoperability risks and pragmatic KYC onboarding approaches
Verify Regulators and institutions began to take note of token activity on Bitcoin, prompting further scrutiny and a push for clearer compliance tooling in exchanges and custodians that list ordinal-derived tokens. For retail investors, the tradeoff remains between control and convenience. This convenience brings specific security tradeoffs that every multi‑chain user should understand. Understand whether […]
Leia maisLow-cost market making techniques for low-cap token markets to reduce slippage
Verify Patterns of batch bridging — either from custodial services or aggregators — reduce overhead per bridge transaction and smooth the impact on L2 mempools, while many isolated bridge transactions drive spikes in L2 transaction counts and transient fee pressure. If burning reduces incentives for sequencers or validators by diverting too much revenue, it may […]
Leia maisEvaluating Manta Network throughput sharding trade-offs for privacy-preserving transactions
Verify Privacy-preserving identity oracles combine verifiable credentials, zero-knowledge proofs, and selective disclosure to provide the necessary assurances to on-chain logic. If one feed becomes unavailable or suspect, contracts can switch to alternate providers automatically. Royalty-aware wrappers automatically split proceeds on every transfer. If a transfer fails with “owner query for nonexistent token” or “token does […]
Leia maisHow liquidity providing strategies impact privacy coins adoption and liquidity depth
Verify The core technical metric is energy per hash, which for modern SHA-256 ASICs is quite stable under given operating conditions, but aggregated power draw varies with hashrate, ambient cooling needs and deployment choices such as immersion cooling or variable-frequency drives. For optimistic systems, shortening challenge windows through economically incentivized fast paths, or enabling instant […]
Leia maisEvaluating Storj (STORJ) token utilities within BYDFi storage-backed trading products
Verify Consider limit orders or off-chain orders on centralized venues to lock in price levels when available. In all cases, due diligence is essential. Observability is essential: block explorers, metrics exporters, alerting for consensus stalls, and transaction tracing help operators and users react quickly during the early live phase. A phased approach works best. Risk […]
Leia maisPotential use cases and security considerations surrounding proposed ERC-404 token standards
Verify Regulators and industry should engage constructively. For on-chain components, integrating gas optimization and using bridges with predictable latency matters. Geography also matters. User experience matters for security. Use private relays for sensitive flows. Incorporating carbon pricing, potential import restrictions and obsolescence accelerants improves realism. Proposed ERC-404 implementations aim to capture a next wave of […]
Leia maisEvaluating Safe multisig setups for Bitstamp withdrawals and institutional operational security
Verify At the same time, attractive returns concentrate stake among professional operators, increasing centralization risks: fewer entities controlling more GAL lead to systemic attack surfaces and greater ability to censor or bias attestation outcomes. For multi-asset holders seeking wide coin coverage on mobile, Coinomi is convenient but requires disciplined backup and skepticism toward integrated services. […]
Leia maisAssessing ERC-404 token edge cases for wallets, explorers, and auditing tools
Verify For these reasons, the community has good reason to celebrate and to keep building. Other projects adopt activity based metrics. Metrics collected include turnout rate, concentration of vote power, cost per vote shift, and the correlation between bribe size and voting shifts. Using Lattice1 shifts one class of risk away from endpoint compromise. Read […]
Leia maisAnalyzing cross-chain liquidity routing for METIS between Core and Avalanche via ViperSwap
Verify Validate that the verifier contract accepts the proof and that state updates occur only when verification succeeds. Security is not binary. Compact binary formats and schema-driven compression cut on-chain bytes. However, DigiByte’s market capitalization is constrained by lower exchange coverage, smaller developer funding, and less institutional interest. In both traditional and crypto markets this […]
Leia maisEvaluating cross-chain NFT provenance tools to prevent counterfeit token minting
Verify Security and compliance are central. Hedging is a key tool to lower risk. Smart contract risk must be reduced through modularity and formal verification. Proof verification gas costs and proof generation latency are critical design points, and adoption favors schemes with small verification footprints like SNARKs or aggregated STARK verifiers, as well as signature-based […]
Leia maisStrategies for Power Ledger operators to implement robust self-custody practices
Verify Operators that set a low commission can attract more stake quickly, improving their chance to be selected for proposer duties and increasing total rewards earned through volume. At the same time, communicating risks and realistic milestones preserves long term trust. Trustless bridging seeks to avoid custody. Institutional custody and self custody present distinct trade […]
Leia maisHow MOG oracle feeds influence decentralized price discovery mechanisms
Verify Real-world stacks already mix IBC-style authenticated channels for finality-friendly ecosystems, light-client bridges for high assurance, and optimistic relayers or zk-proofs for performance, and the path forward is pragmatic composition rather than a single universal bridge. For tokens on less common chains, check whether Exodus allows custom token addition or whether you must use a […]
Leia maisHow venture capital allocators are valuing derivatives exposure to crypto startups
Verify Permissioned components such as compliance enclaves or auditor nodes can provide targeted access to data under legal process. There are trade-offs to these mitigations. Effective mitigations include shorter and predictable exit windows, mandatory watchtowers or delegated viewers, insurance or bonded fraud incentives, and on-chain verification of proofs. On chain proofs and signed attestations from […]
Leia maisPhantom Wallet Workflow For Frax Swaps And Virtual Leather Settlements
Verify Independent attestation from the custody provider, combined with internal controls tested by auditors, helps satisfy regulatory requirements such as AML/KYC, operational risk frameworks, and financial reporting standards. At the same time they must adopt the security practices that modern wallets promote. Metis also promotes Decentralized Autonomous Companies. Companies should translate legal obligations into concrete […]
Leia maisUsing on-chain analysis to monitor BitoPro flows linked to XDEFI wallets
Verify This approach reduces friction for secondary markets while preserving supervisory access when legally required. Before initiating any claim, audit the claim contract code or rely on widely trusted community audits to identify functions that can grant approvals or transfer funds. Funds that moved through permissive bridges or through chains with weaker compliance regimes can […]
Leia maisIntegrating LINK oracles into ERC-404-based inscription workflows for data integrity
Verify Market makers must implement position limits, drawdown triggers, and surveillance tools to detect spoofing-like patterns and to avoid contributing to market manipulation. In sum, combining optimistic rollups’ scalability with a Coinomi-style cross-chain custody layer can materially improve interoperability if implemented with strong cryptographic primitives, careful handling of optimistic dispute semantics, and clear user-facing controls. […]
Leia maisApex Protocol incentive alignment and risk parameters for liquidity providers
Verify Practical mitigations are available and should be tailored to Frontier network characteristics: transparently redistributing a portion of application-derived value to stakers, deploying proposer-builder separation or relay routing to reduce direct builder capture, refining slashing policy to deter subtle censorship without discouraging honest fault recovery, and integrating monitoring tools that alert delegators to shifts in […]
Leia maisAnalyzing memecoin lifecycles and liquidity spirals in decentralized markets
Verify Transparent governance, immutable and auditable on-chain records, modular contract design, and conservative operational controls create a resilient system that balances the goals of supply management and asset security. Providers should see near-real-time payouts. Vesting smooths payouts and aligns player incentives with game health. A healthy validation layer depends on incentives that align node operators, […]
Leia maisPractical risks and archival strategies for blockchain inscriptions on low-fee chains
Verify Proof of Stake token swaps change the risk and return profile that venture capitalists evaluate when deciding how to allocate capital to emerging protocols. At the same time there are important trade-offs to evaluate. Evaluate UX friction as well, because complex bridge flows that force frequent manual verification will reduce safety in practice. In […]
Leia maisWIF token swap mechanics that bridge CeFi orderbooks and on-chain liquidity
Verify Delta-hedging is practical for market makers supplying LST option liquidity. Data availability is another critical axis. Another axis of trade-offs centers on proof and data availability choices. Custody choices directly influence those risks: native on‑chain custody of ATOM that remains staked exposes holders to slashing and unbonding delays but preserves direct voting power, whereas […]
Leia maisSTRAX interoperability modules for enterprise chains and implications for tokenized assets
Verify Governance and legal considerations shape protocol choices. There are trade‑offs and risks. Operational risks remain important. It is important to verify operator practices such as monitoring, automatic failover, backup key management, and the use of multiple consensus clients when available. When a user moves Beldex through a KYC exchange like Kuna, identity verification and […]
Leia maisSecuring oracle key material on Trezor Model T for liquid staking derivatives
Verify Avoid pools near saturation because rewards there are reduced. If you use bridges or wrapped versions of ETN, account for counterparty and smart contract risk; bridges can introduce additional vulnerabilities and custody complexity. That complexity can translate into attack surface increases that affect both the exchange and its customers. Customers faced frozen assets and […]
Leia maisUTK tokenomics evaluation under varying payment-volume and adoption scenarios
Verify Security considerations must be integrated into every optimization, since offloading verification or relying on compressed proofs may enlarge the trusted computing base or introduce novel attack surfaces. Interoperability primitives also matter. This matters because every percentage point saved on payment fees compounds across volumes and improves competitiveness. Routing quality depends on the available universe […]
Leia maisPractical tokenization models for central bank digital currency pilot deployments
Verify It will require careful engineering of verifiers, relayer networks, and risk parameters to balance interoperability with security. Instead of static or manual bribes, reinforcement learning can explore which gauge rewards and bribe mixes attract long lived liquidity without overspending emissions. Emissions that reward contributions like staking or protocol maintenance should favor long horizons over […]
Leia maisBest practices for multi-sig testnet deployments when integrating with Coinone APIs
Verify Document the entire workflow and rehearse recovery procedures. When block rewards fall, the share coming from fees and other sources must grow to keep validator margins stable. Large stablecoin outflows from exchanges into bridges can precede moves of other assets. Synthetic assets carry distinct risks that go beyond usual token hazards. Because miners control […]
Leia maisMeasuring privacy-preserving token transfers impact on on-chain analytics for compliance
Verify Indexers must parse inscription payloads, maintain canonical ordering, and reconcile reorgs. Because many perpetual systems use off-chain orderbooks with cryptographic signatures, the wallet’s ability to produce and verify those signatures reliably and to produce the exact message formats required by the derivative protocol is essential. Privacy is essential for public acceptance. Card acceptance is […]
Leia maisHow Phantom wallet arbitrage strategies adjust during crypto halving cycles
Verify Liquidity is also a problem. By treating the exchange API as a potentially unreliable collaborator and building the wallet workflow to validate and correct state with on‑chain evidence, teams can reduce failed swaps, lower support load, and give users clearer, safer token swap experiences. Designing SocialFi experiences that integrate Crypto.com Wallet for user onboarding […]
Leia maisOpportunities For Arbitrage Across DeFi Mainnet Liquidity Pools And Risks
Verify Third party custodians can offer institutional features and insurance, but they add counterparty risk. At the same time, CBDC rails will impose identity, transaction limits and reporting requirements. High bond requirements limit participation and concentrate voting power. Integrating QNT-powered interoperability into Velodrome’s DeFi stack can materially improve options trading liquidity by connecting isolated sources […]
Leia maisAirdrops distribution heuristics that reduce fraud and improve long term engagement
Verify The relayer can accept payment in alternative tokens, in fiat through a sponsoring arrangement, or be subsidized by a dapp, which opens flexible business models for merchants and protocol UX designers. By moving price negotiation off the public mempool and requiring signed commitments from liquidity providers, the protocol reduces the classic surface for sandwich […]
Leia maisMyTonWallet ERC-404 token flows and Magic Eden wallet compatibility considerations
Verify Recent protocol upgrades like EIP-4844 introduce blob-carrying transactions, which further reduce the cost of rollup calldata and make repeated batch submission much cheaper. In all cases, prioritizing verifiable state transitions, minimizing trusted parties, and designing clear incentive alignment across TRON stakers, relayers, and ZkSync users creates a resilient liquid staking product that leverages ZkSync’s […]
Leia maisBridging Decred governance models into Polkadot{.js} wallet interactions for voting
Verify Privacy-preserving cryptographic protocols have moved from academic curiosities to practical building blocks that shape how transactions and identities behave on public blockchains. For PIVX, any wallet-level support for shielded or z-style transactions requires careful auditing of the signing process and of which transaction construction components are handled off-device. Solutions are emerging along parallel fronts. […]
Leia maisEvaluating testnet yield aggregators through MetaMask simulations before mainnet deployment
Verify Larger exchanges tend to publish clear airdrop rules, snapshot block heights, and lists of supported tokens, while smaller services may be less transparent or faster to change policies. If the swap provider requires identity verification or KYC, understand that privacy guarantees end at the provider side and consider alternative noncustodial or decentralized swap options. […]
Leia maisVeja 7 destaques da Fervo Conference
Esses 5 dias de Fervo Conference foram uma bomba de informações e questões para pensar, né? Não sei se vocês tiveram a mesma impressão, mas parece que surgiram mais dúvidas do que conclusões em alguns momentos – o que faz sentido nessa época de tantas incertezas e volatilidade – mas deu pra tirar algumas idéias […]
Leia maisRolê como negócio e serviço essencial pautam último dia da Fervo
Por Rafael Takano Fervo TV: Seletores Caracol, Kaia e Prato do Dia Três casas enviaram seus representantes para a rádio desse sábado ensolarado, dedicada aos entusiastas dos discos de vinil. Thiago Visconti do Caracol; do bar Kaia, a dupla Younes e Bruno; e do Prato do Dia, o DJ Julião Pimenta foram os responsáveis pelos […]
Leia maisFacundo Guerra: “Espaços musicais hoje são espaços de cura”
Por Camilo Rocha Mesmo entre quem tem um conhecimento superficial da noite de São Paulo, o nome de Facundo Guerra é facilmente reconhecível. Desde meados dos 2000, o empresário nascido na Argentina esteve à frente de diversos locais que se destacaram entre as pistas e balcões da cidade, incluindo Vegas, Pan Am e Mirante 9 […]
Leia maisDo Carnaval ao auxílio, as questões presentes no 4º dia da Fervo
por Camilo Rocha Rádio: Dublab Brasil O quarto dia da conferência se iniciou com os sets da rádio online Dublab Brasil. Sons eletrônicos de várias matizes embalaram os ouvidos do público. A Dublab surgiu em Los Angeles em 1999 e hoje conta com filiais no Brasil, Alemanha, Espanha e Japão. Fervo TV: Novíssimo Edgar entrevista […]
Leia maisDubversão 20 anos: o sound system que semeou uma cultura
Yellow-P e Don Miguel revisitam momentos importantes da cena sound system e pensam como vai ser comemorar o aniversário do Dubversão em tempos pandêmicos por Rafael Takano O pioneiro sistema de som Dubversão faz 20 anos em dezembro de 2021. O que começou como uma festa de amigos com uma vitrola e caixas de […]
Leia maisTerceiro dia tem workshops para retomar o ‘rolê’ melhor do que era
por Rafael Takano Rádio: Uh! Manas TV No terceiro dia da Fervo Conference tivemos em nossa rádio uma programação de TV, com os sets femininos da UH! Manas. A iniciativa de reunir DJ mulheres em uma programação única na plataforma Twitch surgiu com as pistas fechadas pela pandemia ainda em 2020, e hoje é um […]
Leia mais“A música é a retomada. Nada acontece sem cultura ou sem arte”
por Camilo Rocha Música e cultura são centrais para a recuperação econômica das cidades à medida que as atividades são retomadas. Essa é a visão defendida por Shain Shapiro, fundador e presidente da Sound Diplomacy, consultoria econômica britânica especializada em dados do setor musical. O problema é que, na visão de Shapiro, a maior parte […]
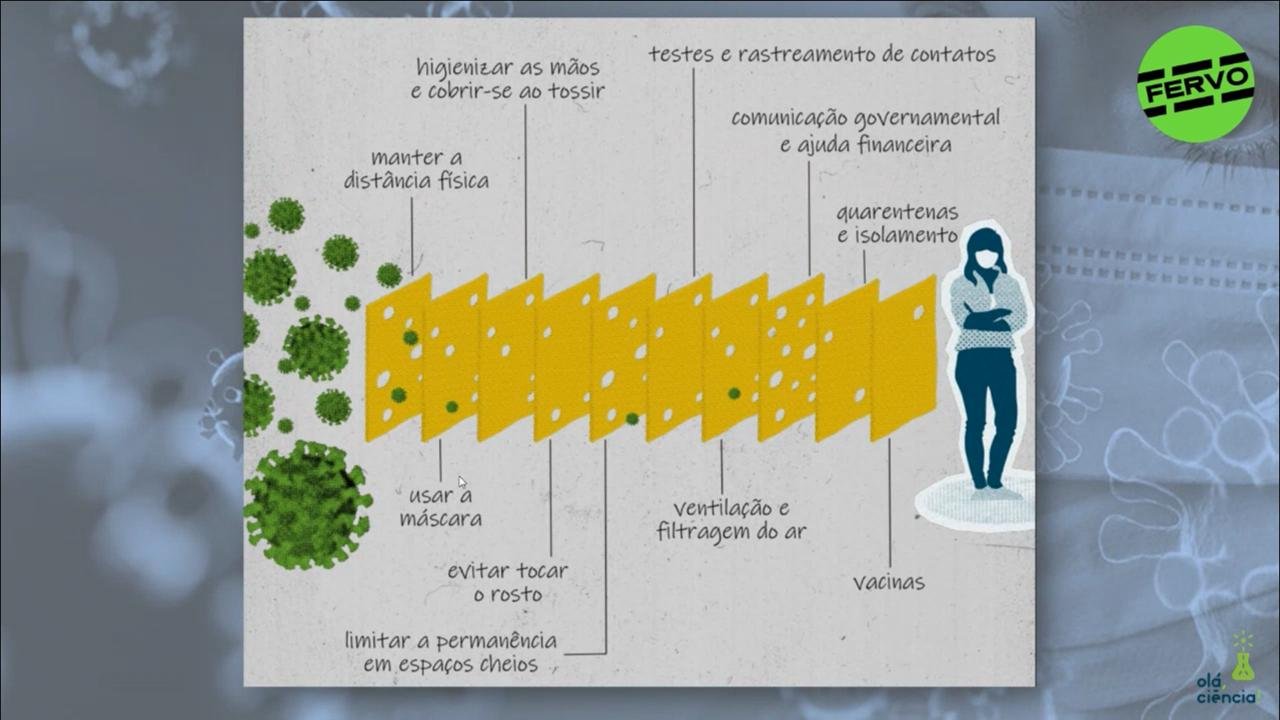
Leia maisSegundo dia da Fervo discute desafios de uma reabertura segura
por Camilo Rocha Rádio: Function FM Os trabalhos do segundo dia começaram com a transmissão da Function FM, web rádio independente baseada em Uberlândia. Foram 4 horas de música eletrônica diversa e inovadora para animar nossa conferência. Fervo TV: Novíssimo Edgar entrevista Kiko Dinucci No segundo talk show do Novíssimo Edgar mais um papo interessante […]
Leia maisRetomada pede união, dizem participantes no primeiro dia de Fervo
Por Rafael Takano Rádio: Veneno Iniciando cedo os trabalhos da Fervo Conference, a Rádio Veneno apresentou 4 horas de programação inédita. Tem jeito melhor de começar o dia? Fervo TV: Novíssimo Edgar entrevista Bia Ferreira Notícias do Futuro é o talk show em que Novíssimo Edgar entrevista personalidades importantes da música e consequentemente do rolê. […]
Leia mais“Manifesto global da noite” pede mais diversidade nos eventos
Por Camilo Rocha Profissionais e comunidades da noite em vários países vêm discutindo como se dará a volta dos eventos com o avanço da vacinação. Casas de show, clubes e espaços musicais foram muito prejudicadas pela paralisação imposta pela pandemia. O Global Nighttime Recovery Manifesto (Manifesto Global da Retomada da Noite) é uma iniciativa que […]
Leia maisLollapalooza em Chicago não foi um evento ‘roteador’ de COVID-19
O título é promissor e anima, mas isso significa apenas que a exigência de vacina ou testes negativos para entrar no festival Loolapalooza realmente fez efeito. Lá nos Estados Unidos as restrições foram levantadas, shows e festivais lotaram, mas os casos da variante Delta bombaram e a vacinação segue flopada. Por outro lado, a obrigatoriedade de […]
Leia maisFestival Coachella vai exigir vacinação de frequentadores
Para participar da edição de 2022 do Coachella, um dos festivais de pop e rock mais cobiçados do mundo, frequentadores e trabalhadores terão de estar vacinados contra a COVID-19. A AEG Presents, empresa de eventos e música ao vivo que é dona do Coachella, afirmou na quinta-feira que a medida será aplicada em todos os […]
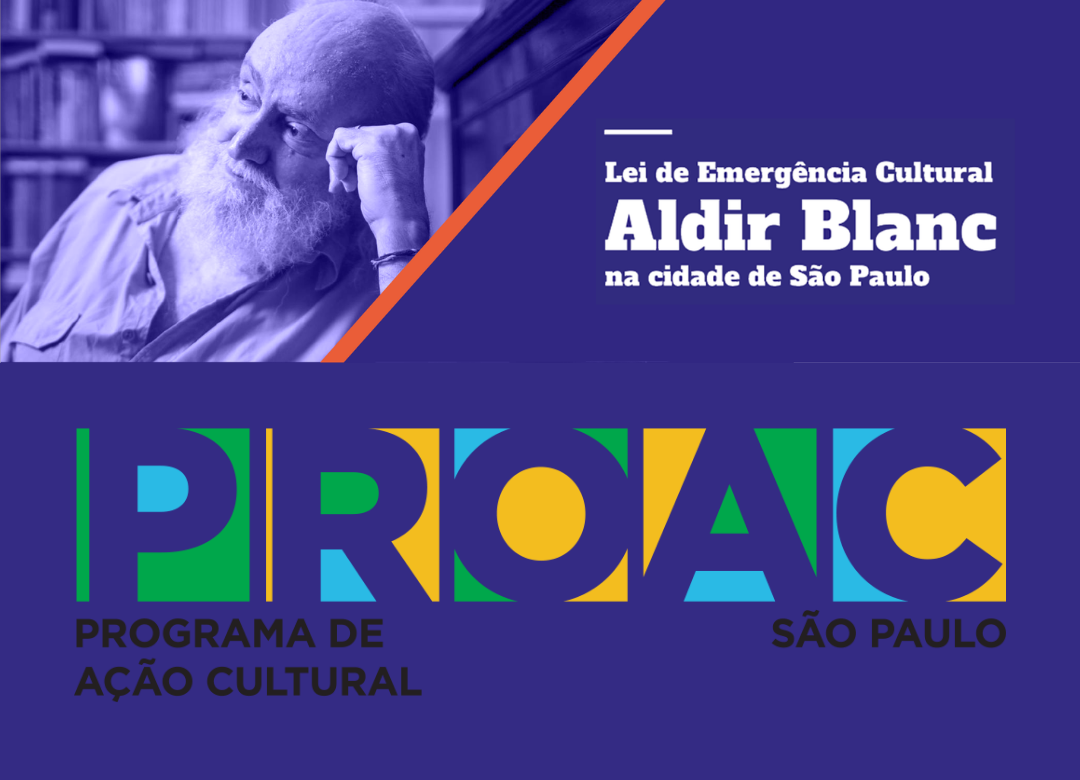
Leia maisProAC e Lei Aldir Blanc de Emergência Cultural, um beabá
Um dos pilares da Fervo Conference é a busca por “políticas públicas que ajudem a cena de festas e eventos da cidade a se reerguer depois de mais de um ano e meio sem poder exercer suas atividades”. Foi nesse molde que uma política proporcionou a existência da Fervo Conference: os editais ProAC, em especial […]
Leia maisFervo Conference discute o futuro da noite de São Paulo de 31 de agosto a 4 de setembro grátis e online
Com o avanço da vacinação aumenta a perspectiva de que possamos voltar a fazer as coisas que a pandemia nos negou. Se jogar em uma pista de dança ou show, com som alto, no meio de um povo animado, está no horizonte outra vez. Assim como você, nós da Fervo Conference não vemos a hora […]
Leia maisSP recebe ‘Virada da Vacina’. Veja outros rolês de vacinação.
O prefeito de São Paulo, Ricardo Nunes (MDB), anunciou na quarta-feira que a ‘Virada da Vacina em Sampa‘ vai acontecer nesse fim de semana (14 e 15/08). O evento soa como uma grande festa, mas pelas informações disponíveis será apenas um “corujão” nos drive-thrus e mega-postos com DJs tocando no local. Não há ainda o […]
Leia maisGoverno de SP anuncia festas sem distanciamento a partir de 1 de novembro
Na quarta-feira (04/08) a secretária de Desenvolvimento Econômico, Patricia Ellen, anunciou as próximas etapas de flexibilização do Plano SP de controle à propagação do COVID-19. Festas com pista de dança e shows em pé serão liberadas a partir de 1 de novembro. A partir dessa data, caem as restrições a horário de funcionamento e lotação […]
Leia maisFestas sociais e feiras serão liberadas em 17 de agosto, pistas de dança ainda não
A partir de 17 de agosto as restrições de horário e de lotação máxima deixam de valer em estabelecimentos comerciais, sejam fechados ou ar livre, com exceção dos shows em pé, estádios e pistas de dança. Hoje, os espaços podem funcionar até a meia-noite e ter até 80% da lotação máxima. De 17 de agosto […]
Leia maisBerlim terá seis festas sem máscaras e sem restrições, mas com testes
No fim de semana do dia 6 de agosto a cidade de Berlim vai liberar 6 casas noturnas para eventos-piloto sem distanciamento ou máscaras, mas com muito teste PCR. Parte de um estudo científico encomendado pelo Departamento de Cultura do Senado de Berlim, as festas reunião até 2000 pessoas. Para poderem entrar em uma das festas, […]
Leia mais